
Unparalleled Security and Trust with Varicent
Protecting your data is our priority. We adopt an iron-clad, enterprise-wide security program, adhering to industry-leading practices and frameworks to keep our customers safe.
Committed to Protecting Your Data
We know how important your data is. That is why we take great care in ensuring the privacy, security and confidentiality of our customers and visitors. Trust knowing your data is protected with Varicent.
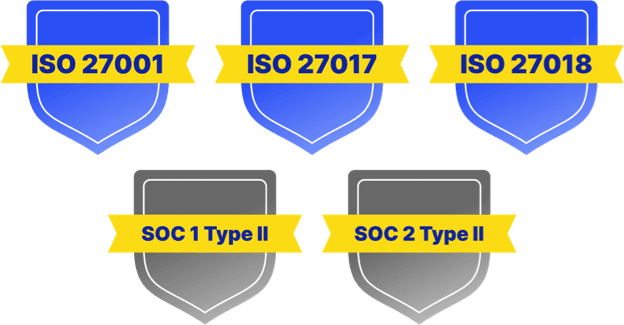
Compliance and Certifications
Our comprehensive third-party compliance program includes annual certification and evaluation of our products, infrastructure, and policies against stringent security requirements and leading industry frameworks.
Elite Defense-in-Depth Security Strategy
We adopt a Defense-in-Depth (DiD) strategy that uses multiple layers of security for holistic protection while continuously monitoring our assets across the technology stack. Varicent's reliable, world-class DiD architecture protect the confidentiality, integrity, and availability of your data. We leave nothing up to chance.
Privacy Regulations
Varicent is a Data Processor and aligns its practices to a variety of privacy regulations. We are committed to assisting customers in achieving and maintaining compliance against applicable privacy laws such as General Data Protection Regulation (GDPR), and California Consumer Privacy Act (CCPA).
Enterprise Security Program
Our enterprise security program includes, but is not limited to, infrastructure and application vulnerability management, secure authentication and authorization mechanisms for all systems, formal security incident response program, NIST-approved cryptographic algorithms, third-party penetration testing, and more.
Varicent Security Features
A high level overview of our security features and functions
Policies & Procedures
- Enterprise Information Security Policy
- Infrastructure Hardening Procedures
- Third Party Risk Management
- Compliance Procedures
Security Awareness
- Regular Security Awareness Training
- Phishing Campaigns
- Security Newsletters
Physical Security
- Hosted on top-tier data centres adhering to internationally recognized standards and frameworks
Perimeter Protection
- Intrusion Detection and Prevention
- Traffic Control
Network
- Virtual network degregation and NAT
- Encryption in-transit
- Logging and monitoring
- Data loss prevention (DLP)
Host
- Hardening in accordance with industry standards
- Infrastructure vulnerability management
- Anti-virus and EDR
- OS patching
- Logging and monitoring
Application Security Features
- Secure authentication and authorization
- Secure code development and QA
- SAST and DAST code scanning
- Web application firewall (WAF)
- Logging and monitoring
Data Security Features
- Encryption at rest
- Backup and recovery
- Secure Integration Solutions with Third-Party Systems
Get Started Today
High-performing revenue organizations have a game plan for growth. Get yours with Varicent. Learn how by booking a demo.
